| Track: | GDPR |
|---|---|
| When: | Thu PM-1 |
| Where: | Portland |
| Organizers | Ann-Marie Grace Ann-Marie Grace |
| Participants | Goher Mohammad Goher Mohammad , David Cervigni David Cervigni , Felipe Zipitria Felipe Zipitria , Francois Raynaud Francois Raynaud , Imran Mohammed A Imran Mohammed A , Jim Newman Jim Newman , Manuel Almeida Manuel Almeida , Mario Platt Mario Platt , Mark Regensberg Mark Regensberg , Paul Dubourg Paul Dubourg , Thomas Franceschini Thomas Franceschini , Tony Richards Tony Richards , Vijay Nair Vijay Nair , Wayne Moore Wayne Moore |
| Remote Participants | Sophie Tonnoir Sophie Tonnoir |
| Invited | Dinis Cruz Dinis Cruz , Fernanda Almeida Fernanda Almeida |
Topic
Practical use of https://github.com/pbx-gs/gdpr-patterns project
What are GDPR Patterns?
They are reusable mappings of data journeys across specific threat modeling scenarios.
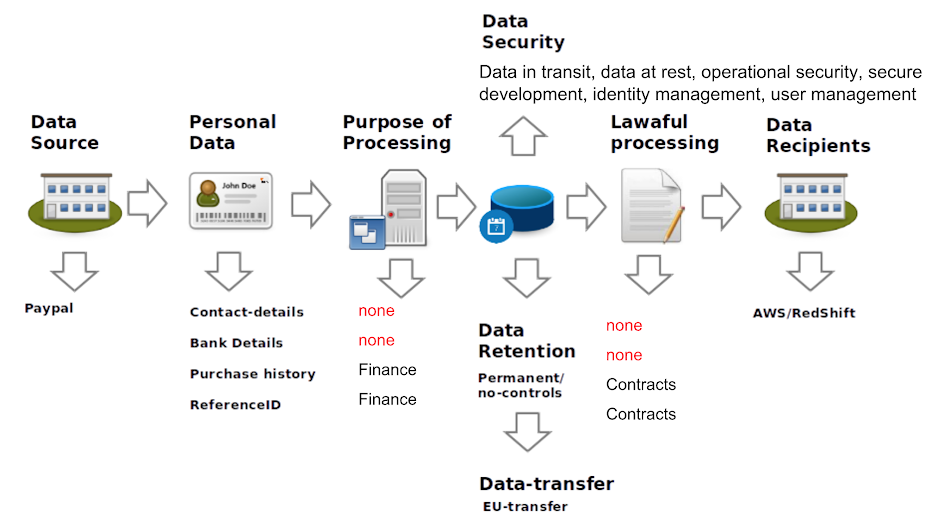
The idea is to take the diagram below and map specific scenarios to it.
‘Based on Threat Models?’
Threat models diagrams are perfect sources of data mappings since they already mapped the flows of data (where it comes from and where they go to)
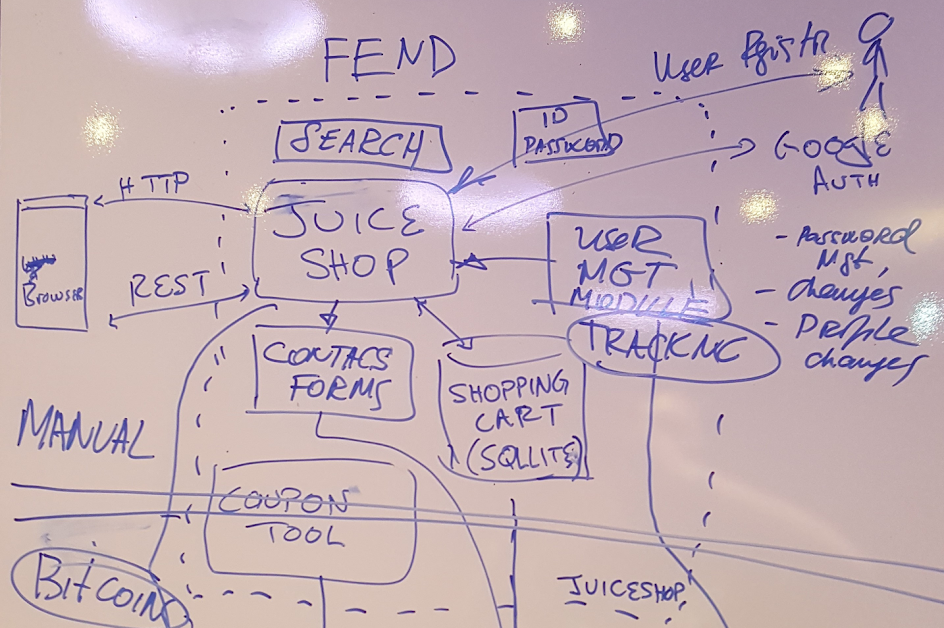
Here is an example of a Threat model created at the last Summit’s Working session on Threat Modeling (on OWASP Juice shop application).
GDPR Pattern driven by Threat Model
Here is an example of what the ‘GDPR Pattern driven by Threat Model’ mapping looks like when it is done (for a service that regularly fetches data from Paypal and feeds it to AWS Redshift).
Maping GDPR Appropriate Security Measures
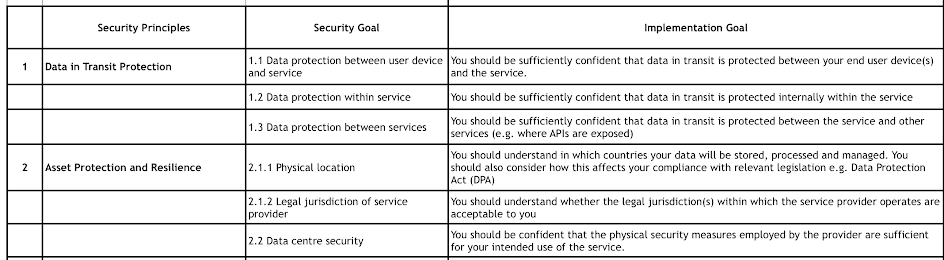
To help with the appropriate security controls, we use this table:
OWASP GDPR Patterns
The GDPR patterns is an OWASP Project and all materials created are released under an open source license, allowing for internal and commercial use.
All content is hosted at the https://github.com/OWASP/gdpr-patterns repo
Register as participant
To register as participant add Hands-on GDPR Patterns to either:
- the
sessionsmetadata field from your participant's page (find your participant page and look for the edit link). - or the
participantsmetadata field from this git session page
Back to list of all User Sessions